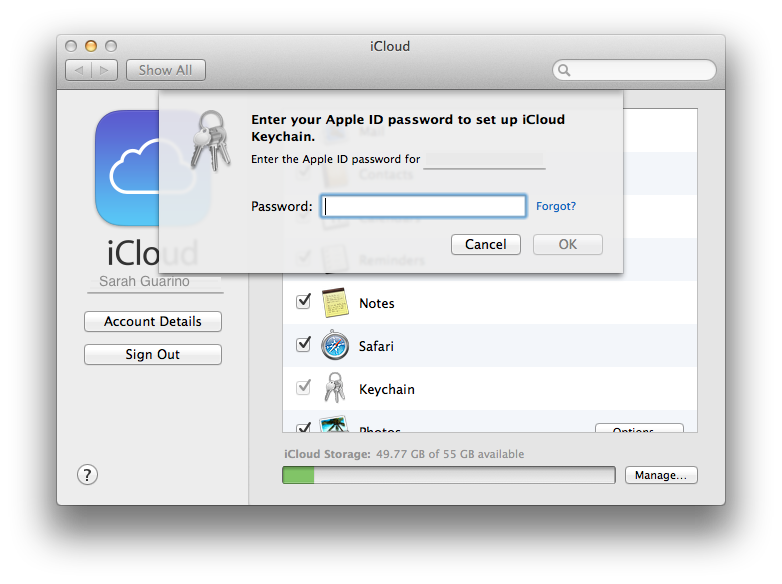
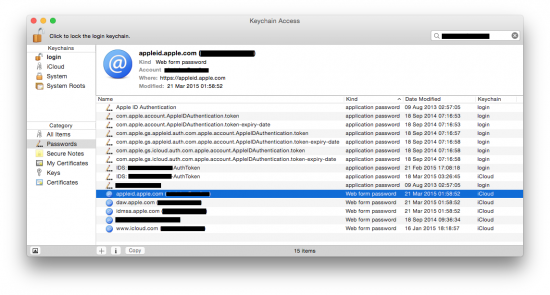
Acquiring and Utilizing Apple ID Passwords, Mitigating the Risks and Protecting Personal Information | ElcomSoft blog
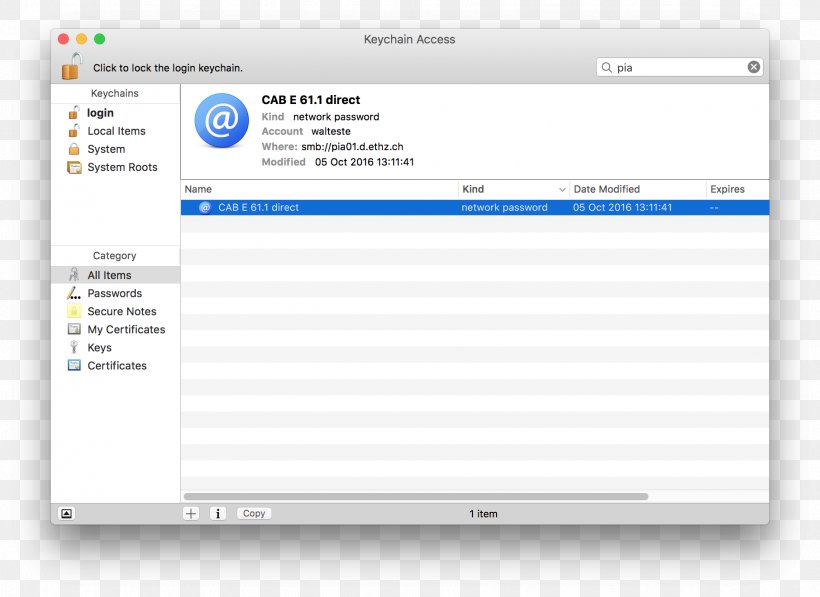
Keychain Access Apple ID MacOS ICloud, PNG, 1812x1320px, Keychain Access, Apple, Apple Id, Area, Brand Download

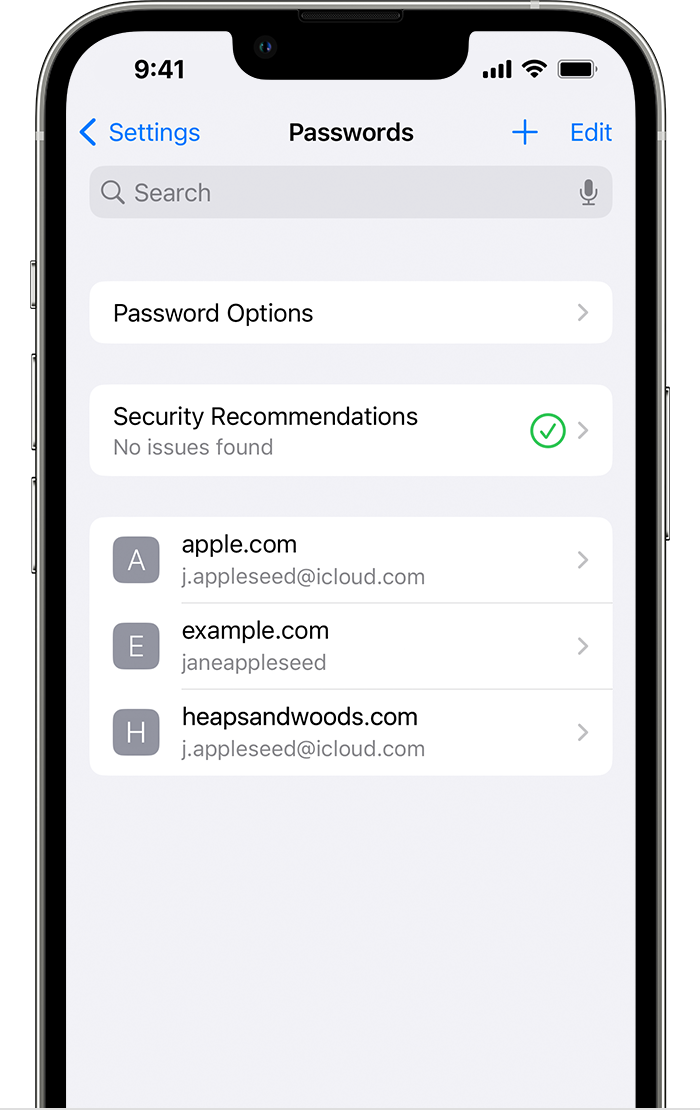
People are just noticing a simple iPhone hack that could save you from a costly nightmare – The Sun | The Sun


:max_bytes(150000):strip_icc()/ScreenShot2021-06-15at10.50.16AM-8586fb20394140ffa1c083e3d785d8b4.png)